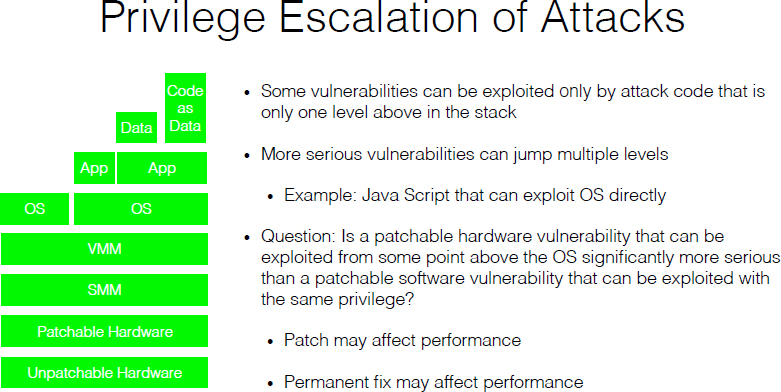
2 Hardware and Software Engineering Assumptions at Risk | Beyond Spectre: Confronting New Technical and Policy Challenges: Proceedings of a Workshop |The National Academies Press

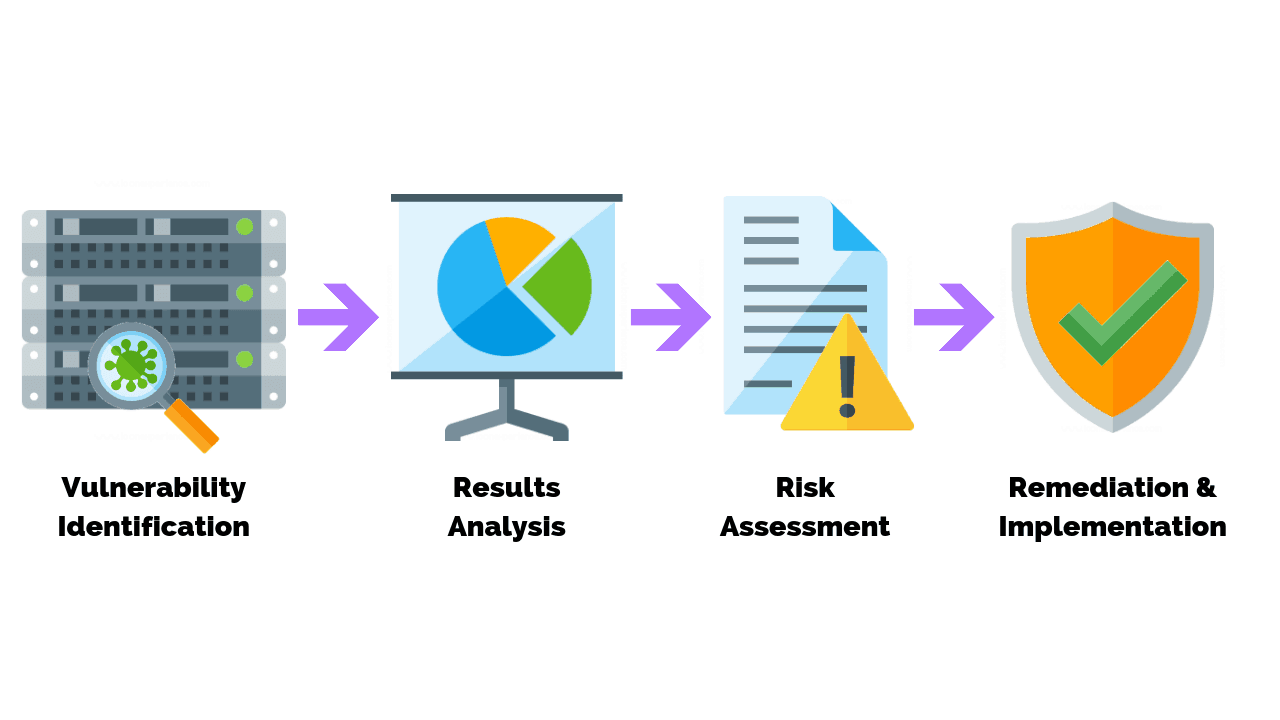
As firmware-level threats continue to gain popularity in the wild, security teams need to understand how these threats work and the real-world risks they pose to an organization's security. Updated for 2021,

A standard IoT model with hardware vulnerabilities. This paper focuses... | Download Scientific Diagram