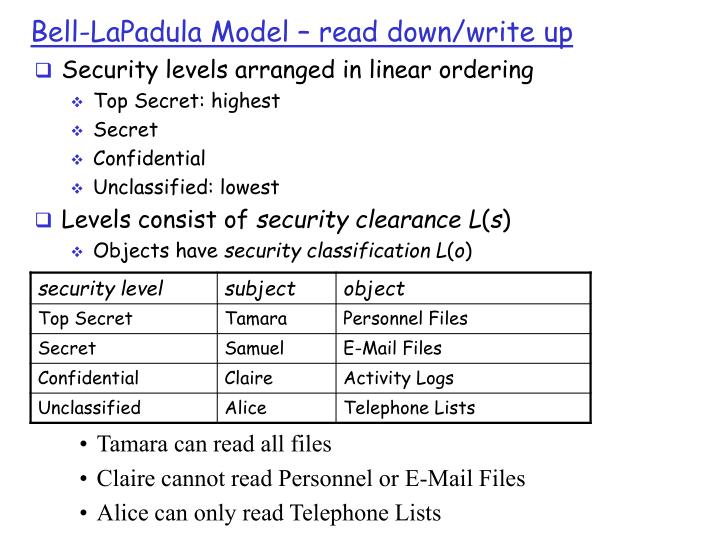
Scalable and secure access control policy for healthcare system using blockchain and enhanced Bell–LaPadula model | SpringerLink
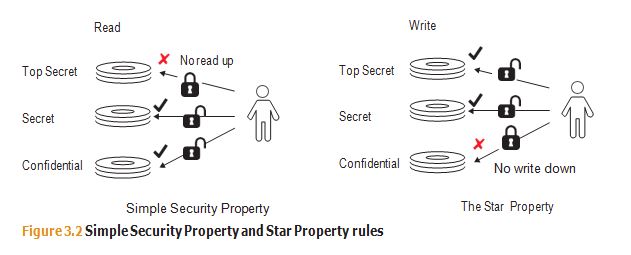
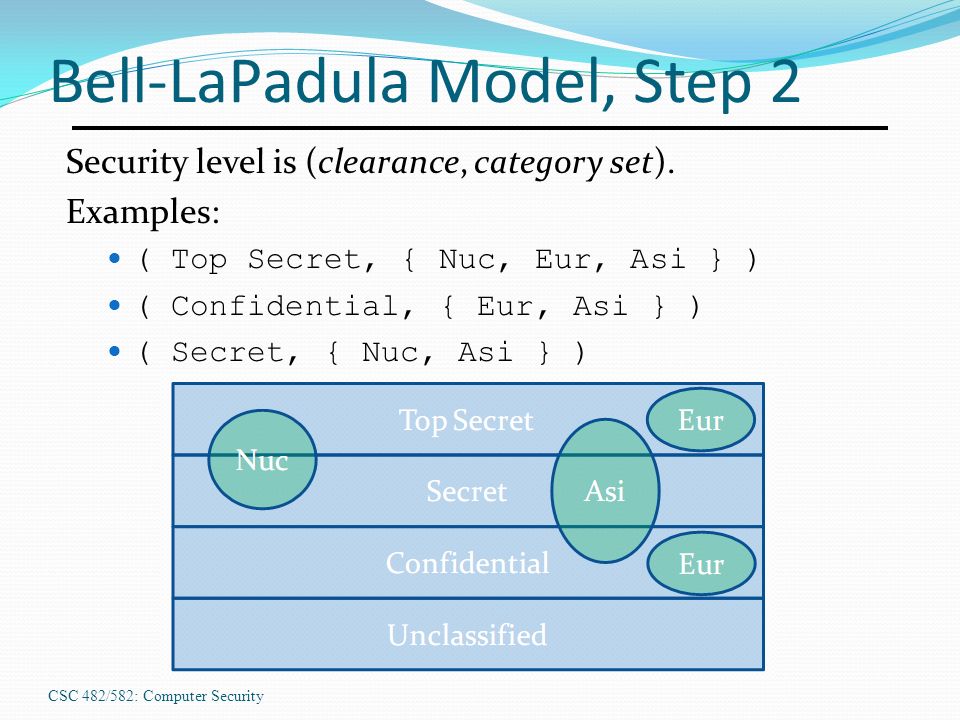
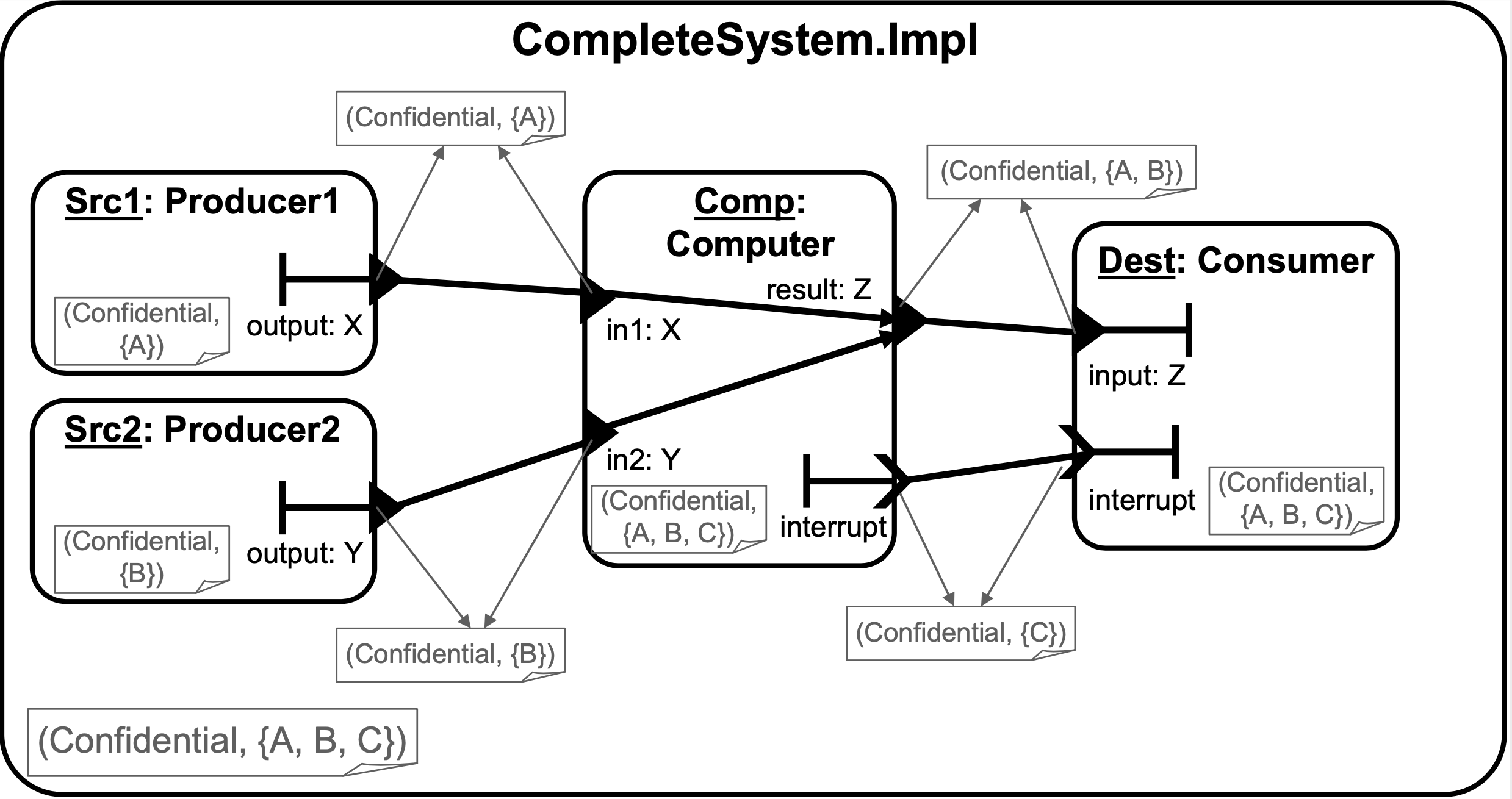
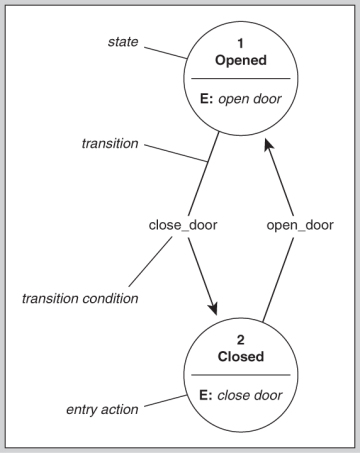
Evaluation of the Appropriateness of Trust Models to specify Defensive Computer Security Architectures for Physical Protection S
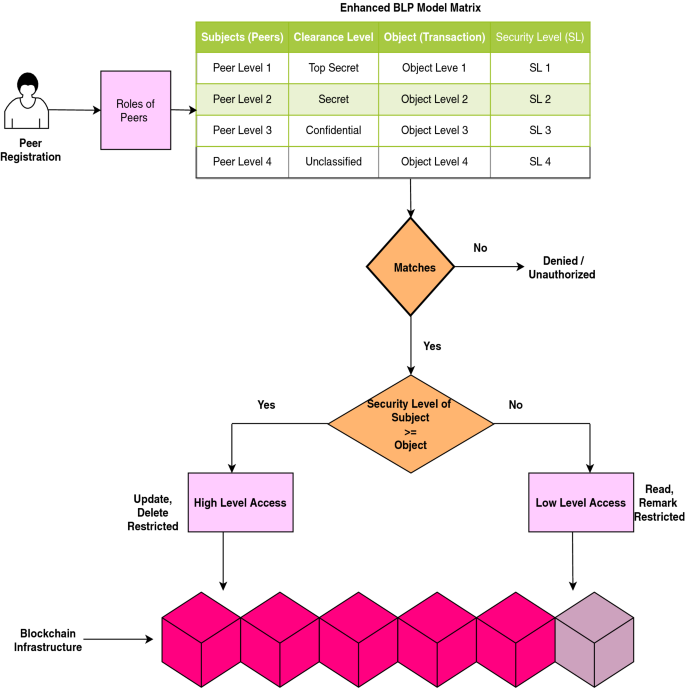
Scalable and secure access control policy for healthcare system using blockchain and enhanced Bell–LaPadula model | SpringerLink

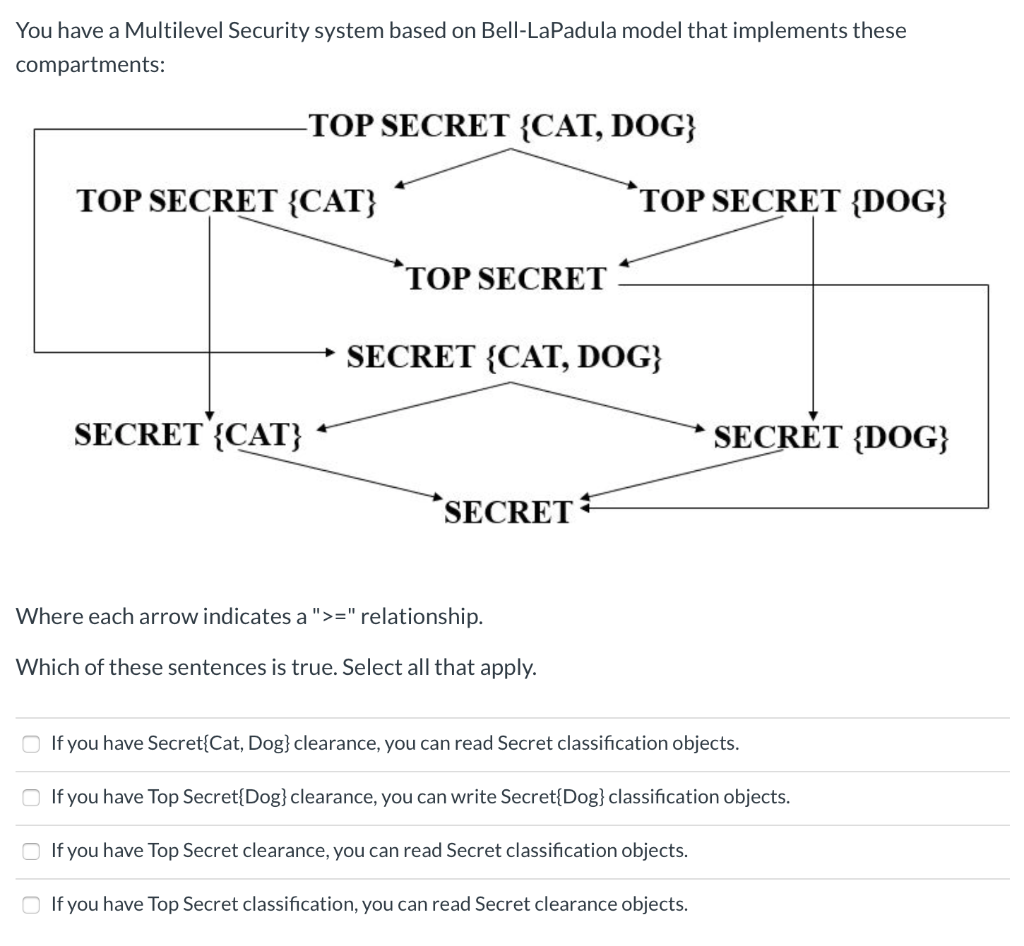
CISSP PRACTICE QUESTIONS – 20210401 by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu

Which form of security model is a mathematically descriptive model that provides upper and lower bounds of authorized access? - Skillset





![Information Security Series: [Part2] Principles of Privileges Information Security Series: [Part2] Principles of Privileges](https://cdn.hashnode.com/res/hashnode/image/upload/v1647290827356/3qC3AeROC.png?auto=compress,format&format=webp)